Video facial recognition systems
Reliable and anonymous
FACIAL RECOGNITION SYSTEM
KNOW THE PROFILE OF YOUR VISITORS

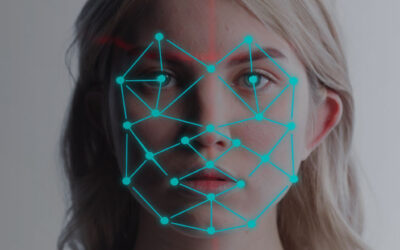
Today it is considered the most natural of all biometrics, and is that we do not recognize ourselves by looking at our fingerprints or iris, but by looking at our face.
The incorporation of facial recognition algorithms in video surveillance systems opens up a world of possibilities, both for security and for the operation of a business.
Facial recognition systems detect, identify and process images of individuals, while making them “anonymous” by transforming them into sequences of zeros and ones, in order to exploit the information from the captured images to the maximum.
With SCATI, thanks to this technology, you will be able to segment the profile of your public by gender and age, identify your VIP clients and offer them a differential treatment. It will also be possible to control the access of your employees and visitors, authorizing or denying access to certain areas or others, or even prevent identity theft anonymously. Todo ello cumpliendo la normativa vigente sobre protección de datos.
Do you want to have information about who accesses your facilities?
Open, comprehensive and scalable
Incorporate as many facial recognition devices as you need. Your needs may change, but you can manage everything from a single video platform.
Centralized management
Proactive system
Advanced Forensic Search
Locate any person in seconds through advanced search filters (faces, names, IDs, etc.) or reference images. Get all the information about your accesses and exits of the facilities.
Bidirectional
The communication between the control centre and the installations is bidirectional, so the information is fluid and updated automatically.
Business Intelligence
With the information collected, a business intelligence system is exploited, accessible by other departments of the organization. They will use the information to produce reports, improve security and business insight.
other solutions

ACCESS CONTROL
Know who accesses each facility and when. Whether they are employees of the organization, suppliers or visitors, access can be on foot or by vehicle, to the building itself or to a specific area of the building.
Discover our access control solutions.
Read more
Protecting history: SCATI security solutions at the Solar Boat of the Grand Egyptian Museum (GEM)
The Solar Boat building at the Grand Egyptian Museum (GEM) faces the challenge of protecting valuable historical pieces. The systems must guarantee constant monitoring and also integrate harmoniously without disrupting the visual experience of visitors or the unique...
Access control trends for 2025: innovation and security
Access control management has seen significant advances in recent years, and 2025 promises to be a key year for consolidating technology and security trends. With both physical and digital threats on the rise, companies need innovative solutions that prioritize...
Biometric technology in access control: the future of security
Discover with SCATI what are the top ten benefits of using access control in your business.
case studies

Access control by facial authentication in corporate environments. The solution is completed with a body temperature measurement system and mask detection to allow access.

The systems identify patients in order to offer them more personalized and differential care.
Combating identity theft in branch offices (Mexico)